4 Most Common Types of Inherent Risks for IT & Cybersecurity
Mitigating inherent risk is a key piece of an effective cybersecurity strategy. To develop a strategy that works for your organization, it's imperative you understand what inherent risk is, how it’s measured, and how it can impact your digital assets.
What is an inherent risk?
In cybersecurity, the term inherent risk refers to the risk that is present before controls or countermeasures are put in place. In other words, inherent risks are vulnerabilities and limitations innate to an organization.
When comparing inherent risk vs. residual risk, the latter includes risks that remain after protections are implemented. Even after you take all the necessary precautions, you're still exposed to certain threats. Residual risks are inevitable due to the dynamic nature of cybersecurity, where new vulnerabilities and attack vectors emerge constantly.
Want to learn more about using a password manager for your business?
Check out Dashlane's password manager for small businesses or get started with a free business trial.
Need more? Check out our enterprise password manager solution.
Types of inherent risks
Inherent risks can be grouped into four main categories:
- Human factors. Human error is the number one cause of breaches. In fact, a staggering 74% of breaches include a human element, according to a 2023 study. Human error can be a result of lax training, but there’s also the issue of negligent and malicious insider threats (aka risks posed to an organization by individuals within it).
- Existing technology. No system is invulnerable to cyberattacks. All software can be penetrated given enough time and resources, while hardware has its own inherent limitations. Existing technology can be an inherent risk, regardless of how advanced and well-protected it might seem.
- Emerging technology. Advanced technologies like artificial intelligence (AI) and the Internet of Things (IoT) are already transforming our society and introducing new challenges. For example, they increase the attack surface available to cybercriminals and, thus, the inherent risk organizations face. To use the power of these technologies for good, security experts can leverage AI tools to analyze large data sets, identify unusual patterns or malicious behavior in real time, and automate security responses.
- Environmental factors. External circumstances must also be taken into consideration. From floods, climate-change-induced disasters, and power outages to political instability, environmental factors play a big role in cybersecurity. Failing to account for these factors when developing a cybersecurity infrastructure can lead to major issues down the road and irreparably compromise an organization's ability to safeguard its assets.
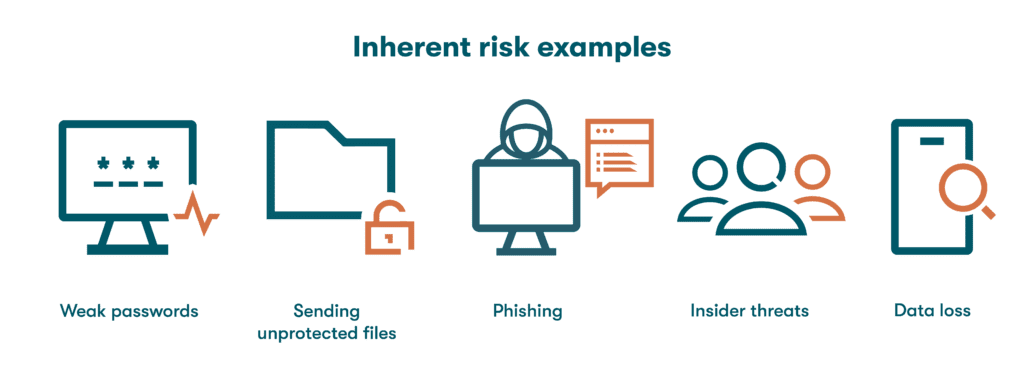
Inherent risk examples
Online activities carry a certain amount of inherent risk to cybersecurity. Fortunately, for the examples below, it’s possible to take steps to reduce that risk.
- Weak passwords can enable unauthorized access, stolen data, and more. Passwords that are reused and easily guessed are faster to crack. Unique and complicated passwords, on the other hand, reduce your vulnerability.
- Sending unprotected files can result in data loss or theft. Man-in-the-middle attacks intercept and exploit unprotected files. To avoid this risk, get in the habit of encrypting files and only sharing passwords using secure, encrypted methods.
- Phishing can easily lead to malware and stolen passwords, and AI is only making it easier. AI chatbots can generate grammatically correct phishing messages in a mere second. Deepfake technologies can also create remarkably convincing replicas of an individual's voice or appearance. Using passwordless technology like passkeys and reducing your digital footprint (by regularly deleting cookies, outdated files, and inactive email addresses and social media accounts) helps to reduce this risk.
- Insider threats involve any attempt by an employee or other member of your organization to compromise sensitive information. They may be motivated by personal gain or by outside actors. The right way to prevent this kind of threat is through an intelligent system of privileged access, as well as promoting a strong company-wide culture of security.
- Data loss can take place with or without malicious intent. For example, an employee may accidentally delete or overwrite an important file because they were given a higher level of access than their role requires. Companies can mitigate this risk through proper information training, implementing least-privilege access rights, and making adequate backups of their files.
Factors that increase or decrease inherent risk
When it comes to cybersecurity, several factors impact the level of risk:
- Certain industries have higher stakes because they involve large amounts of capital, data, or intellectual property. To a cybercriminal, the allure of a successful attack can be worth the potential penalty. Industries such as finance and healthcare are often highly regulated to reduce and mitigate cyber crimes.
- System complexity affects an organization’s ability to defend against attacks. Complicated systems can have more vulnerabilities and access points for hackers.
- Risk-based cybersecurity reporting is an approach to cyber preparedness that prioritizes the most at-risk areas of your system. Mature software systems are often too big and complicated to protect in their entirety. By focusing on areas that are more likely to be attacked and have greater consequences if attacked, IT professionals can reduce overall risk as efficiently as possible.
- An organization's culture of security has a significant impact. Most successful hacking attempts are feats of social engineering. An organization is better protected when its employees are aware of possible threats and know how to respond to them appropriately.
How to measure inherent risks
While the vast majority of organizations have some protections in place, inherent risk assessment is key to developing a robust cybersecurity strategy and infrastructure.
Conducting an inherent risk audit revolves around assessing threats to an organization's digital assets as well as identifying vulnerabilities. This can be achieved in six steps.
- Assess systems and processes
Inherent risks can only be measured if systems and processes in an organization are identified first. This calls for a comprehensive evaluation of essential components such as software, hardware, and network infrastructure. - Identify and rate threats
The next step is to identify and prioritize potential threats, which can be internal or external. Accidental data leaks and employee negligence, for example, would be internal threats. External threats can range from ransomware to cyber espionage. - Identify and rate vulnerabilities
Once you consider the threats, you need to look at vulnerabilities as well. Gaps, weaknesses, and other security holes should be assessed to determine the extent to which they could be exploited by a threat actor. - Estimate the likelihood of exploitation
What is the probability of an attacker successfully exploiting a vulnerability? Would they need to carry out a complex attack, or would a rudimentary phishing campaign do the trick? Are there budgetary concerns that need to be considered? The likelihood of exploitation can't exactly be quantified since success depends on countless factors, but once you've identified potential risks, you should be able to get an idea of which are more or less likely to be exploited. - Determine risk rating
Determining risk ratings is the final step. This can be a rather complex process, but it can be stripped down to the following equation: Risk rating equals likelihood of exploitation plus magnitude of impact.
Imagine a small e-commerce business that doesn't have the best security measures in place. They discover vulnerabilities with a high likelihood of exploitation. If the business were breached, customers' personal data and credit card numbers would be exposed, so the impact would be severe. A threat like this would have a high to severe risk rating. - Estimate the magnitude of impact
Consider each scenario to estimate how much damage (financial, reputational, legal, etc.) a competent threat actor could do. Approximating the impact of a successful attack can help you prioritize mitigating the activities with the greatest potential damage.
“Our strongest tools are our reputation and relationships. A breach could do more than take our security; it could remove the trust from our name that we’ve worked so hard to build.”
What to do after identifying inherent risks
Identifying inherent risks sets a solid foundation for developing an effective cyber defense strategy. Here's what to do after identifying those risks.
Develop and implement a risk mitigation plan
Cybersecurity is centered around risk mitigation: prevention, detection, and remediation. Prevention may involve the implementation of access controls, employee trainings, and encryption. Detection involves monitoring for unusual patterns, whereas remediation is all about resolving the aftermath of a breach or attack.
Communicate results and policies
Open communication and transparency can make all the difference, especially in large companies that operate in dynamic environments. Depending on the scope of the identified risks, this communication could take many different forms. You may opt for company-wide meetings or online trainings, or you might start by focusing on specific departments that are most at risk.
Measure progress and reassess
Risk mitigation needs to keep pace with evolving cybersecurity threats. What was a sound strategy yesterday could prove insufficient to prevent today's attacks. Measuring progress and regularly reassessing an organization’s security threats and posture can make all the difference.
How Dashlane helps mitigate inherent risk
The identification and measurement of inherent risk is crucial precisely because it allows organizations to assess potential vulnerabilities and threats before any security measures are implemented. Once a business gauges inherent risk, it can efficiently decide where to allocate resources and which controls, security policies, and mitigation strategies to prioritize.
Dashlane provides powerful insights and tools to support inherent risk management. An intuitive Password Health score identifies opportunities for employees to improve weak or reused passwords and provides a quantifiable measurement for managers. Plus, the user-friendly tools, including a Password Generator, Autofill, and a secure password-sharing portal, promote adoption and a healthy culture of security amongst employees. With the industry’s first in-browser passkey solution, AES 256-bit encryption, a zero-knowledge architecture, and more, Dashlane effectively mitigates authentication risks for more than 20,000 organizations worldwide.
Cyber threats may seem impossible to keep up with, but with the right tools in your tech stack, you can feel more confident in your organization’s security this year.
Discover how to conduct a security audit, and start your free Dashlane Business trial today.
References
- Dashlane, “Cybersecurity Strategy: Best Practices for Small-to Medium-Sized Businesses,” October 2022.
- Verizon, “2023 Data Breach Investigations Report,” 2023.
- Dashlane, “A Complete Guide to Managing Technology Risk at the Enterprise Level,” July 2023.
- Dashlane, “How Password Reuse Leads to Cybersecurity Vulnerabilities,” May 2023.
- Dashlane, “Excel Spreadsheets: How to Password Protect Your Excel Files,” July 2023.
- Dashlane, “Deepfakes Are Getting More Realistic—Here’s What it Means for Online Security,” September 2023.
- Dashlane, “5 Pros & Cons of a Future Without Passwords,” October 2023
- Dashlane, “What Is a Digital Footprint and Why Is It Important?” August 2023.
- Dashlane, “How to Create a Culture of Security,” March 2022.
- McKinsey & Company, “The risk-based approach to cybersecurity,” October 2019.
- NIST, “Guide for Conducting Risk Assessments,” September 2012.
- Dashlane, “These New Alerts Notify You When Something’s Phishy,” September 2023.
- Dashlane, “A Comeback Story: How JD+A Spotted Their Compromised Passwords and Secured Company and Client Data,” May 2022
- Dashlane, “What To Do If a Scammer Has Access To Your Email Address,” April 2023.
- Dashlane, “Everything You Need to Know About Your Password Health Score.”
- Dashlane, “Putting Security First: How Dashlane Protects Your Data,” October 2023.
Sign up to receive news and updates about Dashlane
