The average employee uses 40–60 apps, but only around half of those apps are currently behind single sign-on (SSO). Without the right tools, a lot of productivity is lost on creating unique passwords, logging in, and resetting forgotten passwords.
SSO technology can improve efficiency and the user experience without compromising a company’s cybersecurity.
Let’s explore the technology behind SSO, how it works, and what tools can integrate with SSO to make an organization’s cybersecurity even stronger.
The technology behind SSO
SSO stands for single sign-on and refers to systems where a user can log in once and access multiple apps or platforms through that single sign-on. SSO is an authentication method that IT can use to grant employees access to the tools they need while restricting them from tools they don’t need or shouldn’t have clearance to use.
On the backend, SSO technology uses authentication tokens, which function similarly to getting a wristband at a concert. People only need to acquire a wristband once at the door when they first enter the concert, and then the rest of the evening, they’re free to access any vendor within the venue without needing a new wristband.
This authentication token is a piece of digital information that can be stored within an SSO provider’s server or on the employee’s web browser. Any app that an employee attempts to access will first check with the SSO provider, which will then provide the authentication token to the app if the user has signed in (if not, the user will be prompted to log in).
Authentication tokens aren’t synonymous with user identities. This means that SSO technology doesn’t automatically remember who a user is. Instead, SSO verifies a user’s identity by matching their login credentials with their identity in a larger database.
Think of this process like looking through a textbook: you might not automatically know the page number where “the Cambrian Explosion” can be found, but you can access that information easily by referring to the index at the back of the book.
In sum, SSO isn’t necessarily an all-knowing, all-remembering identity management platform, but it works seamlessly with an employee database and the user to simplify the login process throughout an employee’s workday.
How does SSO technology work?
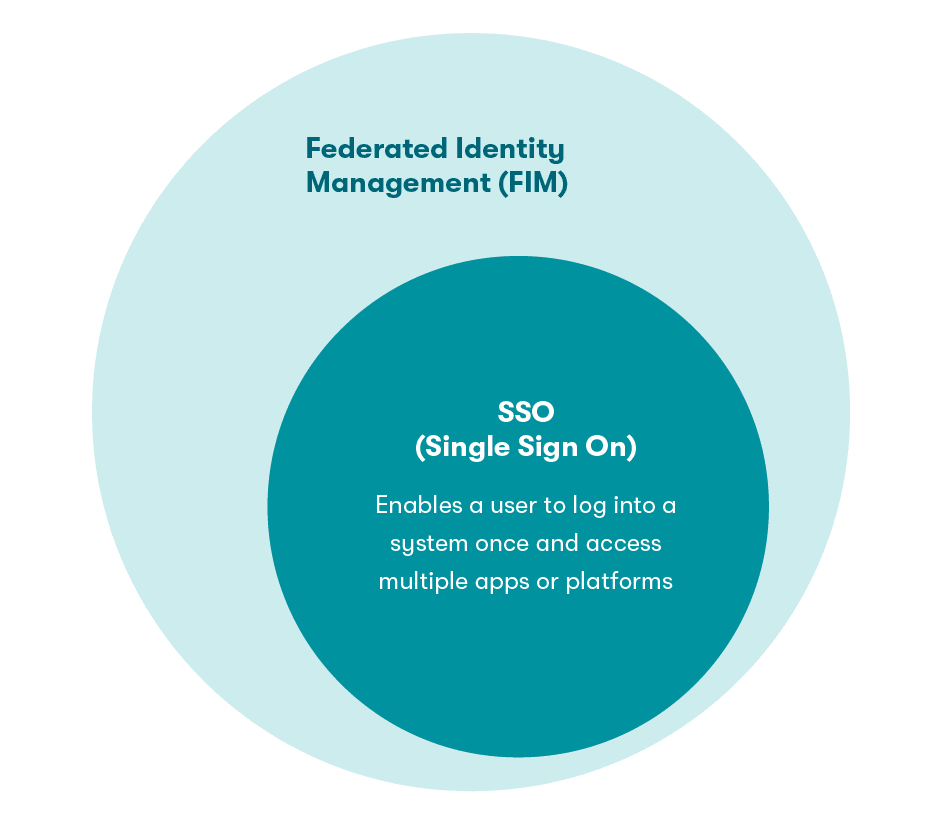
SSO technology is part of a broader security concept called Federated Identity Management, or FIM, which refers to a trust relationship between multiple domains or identity management systems.
Instead of asking the user for proof of identity each time they access a new app, identity management systems and domains figure out a user’s identity amongst themselves without requiring re-authentication.
There are a few different concepts within FIM that work within or alongside SSO:
- OAuth 2.0 falls under the umbrella of FIM tools because it uses that backend trust relationship to allow user identity information to be shared across platforms.
- OpenIDConnect, or OIDC, is the additional layer on top of OAuth 2.0 that brings SSO to life. OAuth 2.0 and OIDC work in tandem to enable SSO.
- Active Directory, or Active Directory Directory Services, or ADDS, is Microsoft’s directory service. Users who are part of ADDS can automatically access other systems that integrate with ADDS. If you recall our textbook analogy, ADDS is Microsoft’s textbook and index; if you show up in the index, you can cruise around to other applications without having to re-authenticate. This is SSO at work.
- Lightweight Directory Access Protocol, or LDAP, defines a way to organize and query a directory and is therefore used in access management and control processes. For example, when a user attempts to access an app, LDAP will be used to query the directory and verify that the user should have access to the application and provides authentication.
Pro tip: Same sign-on, despite the similar name, isn’t the same as single sign-on. Instead of using authentication tokens to communicate across different apps, same sign-on uses the same login credentials across each app. There is no trust relationship between same sign-on and the apps it logs into.
Single sign-on, on the other hand, is trusted by each app and only requires that authentication token.
The advantages of secure SSO technology
Here’s a breakdown of the benefits that SSO can bring to an organization:
- Stronger—and fewer—passwords: When employees don’t have to remember dozens of passwords, they’re more inclined to make that one password much stronger and engage in safe password management.
- Better IT control: SSO gives IT more control over access to business applications and platforms, which helps with shadow IT. Further, with SSO, IT can grant users different levels of access to certain platforms instead of granting permission every time an employee needs access.
- Added security: SSO technology records when and where someone signed on, so IT can easily keep track of extraneous sign-ons outside of an employee’s normal geographic area or at odd hours of the night. SSO also allows for easier 2-factor authentication (2FA), as employees only have to authenticate themselves once.
- More efficient password management: Signing on to all platforms with one set of credentials can reduce wasted time logging into multiple applications and mitigate frustration with password recovery and help desk calls. SSO also allows for a more streamlined process for enforcing password policies throughout the company.
Next-level SSO integration
If you’re interested in further bolstering your organization’s cybersecurity, there are several options that work hand-in-hand with SSO technology.
Password managers
Like SSO, a password manager requires the employee to remember just one password. This single entry point means that login credentials must be strong and secure. Password managers can help further seal the cracks in your employees’ online safety with added security benefits such as:
- Protecting internet browsing for personal use: SSO doesn’t protect work-related apps for personal use, like travel or lunch-hour internet browsing. While SSO is limited to professional apps only, a password manager helps secure all accounts with unique passwords.
- Factoring in cloud-based apps: With the increased adoption of SaaS products and remote work, organizations have shifted to cloud-based apps—many of which aren’t compatible with SSO. Password managers, on the other hand, circumvent the incompatibility of SSO technology with cloud applications.
2-factor authentication
2-factor authentication, or 2FA, provides an invaluable second layer of security when employees use their credentials to log in to an application. By linking an employee’s username with their email address or phone number, 2FA verifies their identity whenever they attempt to access a platform.
Although 2FA would quickly become a pain if an employee had to use 2FA to log on to every single platform throughout the day, SSO eliminates this hassle by only requiring users to complete 2-factor authentication once.
Identity Access Management (IAM) and security information and event management (SIEM) tools
Many employees—especially those who work remotely—use their personal devices to access professional applications from time to time. But this habit, however occasional, can potentially put data at risk.
Identity and Access Management (IAM) enables employees to access the resources that they need when they need them without compromising the safety of their personal and professional data or creating time-consuming hassles for the IT department. IAM automatically creates in-depth audit trails that can help prove compliance and accelerate reporting.
Similarly, security information and event management (SIEM) tools automatically scan events and security data for potential vulnerabilities and security threats before they happen using artificial intelligence and machine learning.
Both IAM and SIEM work in concert with SSO technology to simplify the login process while creating a detailed trail of information about the device, time, and location of logins to identify cybercriminals before it’s too late.
How to implement SSO
Agreeing to transition to SSO as an IT manager is only the first step to a successful deployment across every department. There are two approaches that will be beneficial as you implement SSO technology across your organization:
- Securing management buy-in
SSO isn’t just a benefit to the IT team and employees—it can help protect your company’s bottom line. According to Verizon's 2020 Data Breach Investigations Report, more than 80% of all hacking-related data breaches involve stolen credentials or passwords—and the average cost of a data breach in 2021 was $4.2 million.
Communicating the potential financial pitfalls of data breaches to upper-level management can help convince your organization that implementing SSO could be a long-term financial strategy and, therefore, a necessary component of the company’s operations.
- Educating employees
A successful transition to SSO technology requires that every person within a company is educated on the benefits of the technology and how to use it. Because the average employee has a lot of priorities to manage, framing SSO as a solution that will save them time while keeping their login credentials secure will likely increase SSO adoption.
Establishing a clear password policy for all employees and educating them about safe password practices should go hand in hand with implementing and integrating SSO. This ensures your organization is building a human-first security culture in which employees understand how to maintain good password health and work together to protect themselves and the organization, laying a strong foundation that will be instrumental in supporting the long-term success of SSO.
As an award-winning solution, Dashlane makes life easy not only by simplifying all of your employees’ sign-on process during the work day—it can also help enhance the overall cybersafety practices of your organization.
Sign up to receive news and updates about Dashlane
Related articles

From Security Awareness to Proactive Defense: Dashlane Launches First–of-its-Kind Integration with KnowBe4