Workplace Tips
Workplace security best practices and recent news

How Attackers Think: Understanding Your Attack Surface Before They Do
Learn how attackers find your blind spots before you do and how to map your attack surface and threat model as a security-first team.

MFA Methods Compared: SMS, Authenticator Apps, Hardware Keys, and Passkeys
Not all MFA is equal. Compare SMS, authenticator apps, hardware keys, and passkeys side-by-side. Get a framework for enterprise IT admins to deploy phishing-resistant MFA.
SaaS Sprawl: How to Manage Shadow IT and Unsanctioned Apps
SaaS sprawl creates security blind spots IT teams can’t afford. Learn how to detect unsanctioned apps, run a SaaS audit, and regain access control.
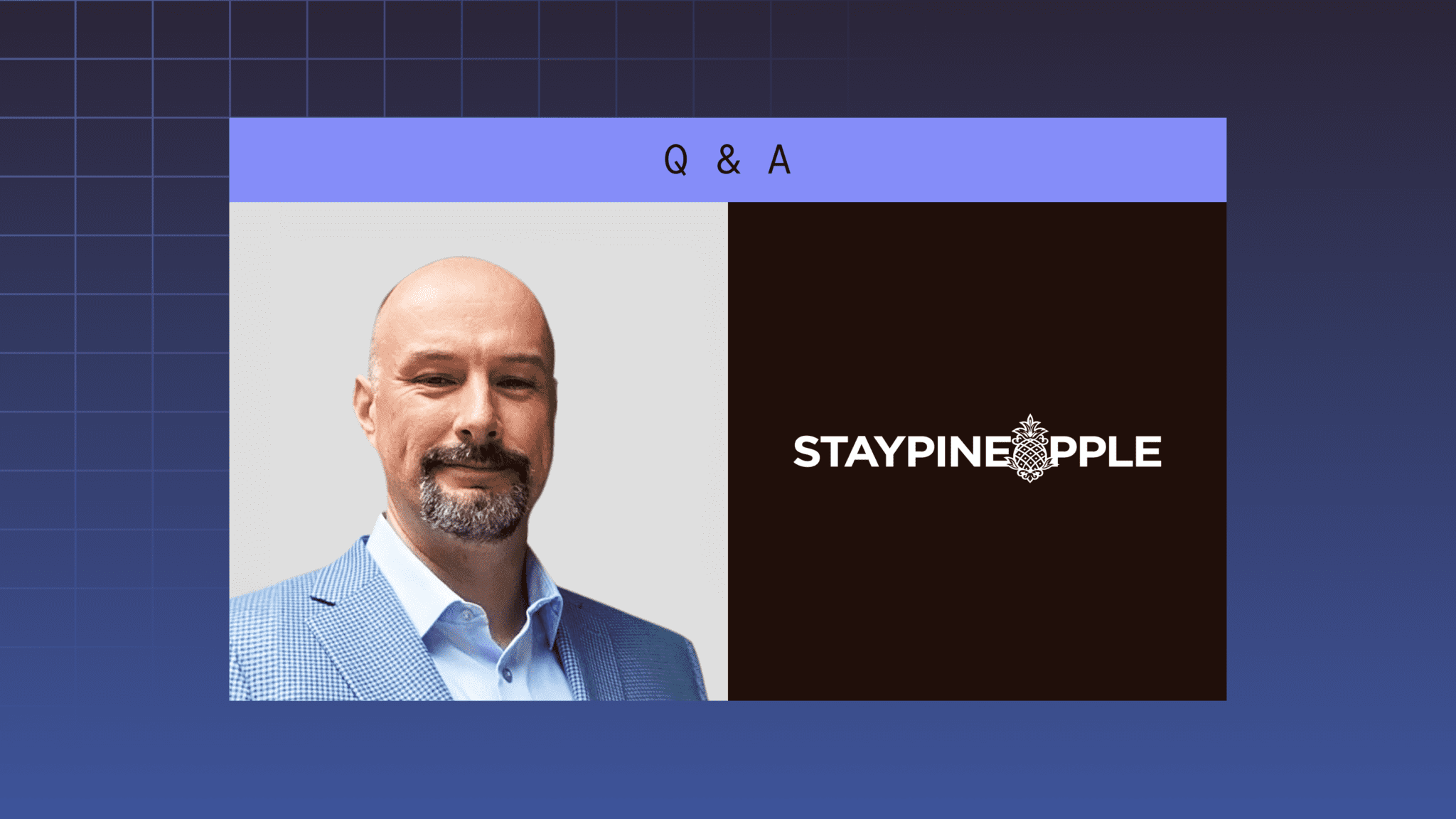
Q&A: How Staypineapple Balances AI Innovation, Access Management, and Security
Struggling to secure credentials while adopting AI? See how Staypineapple’s IT VP governs access, prevents phishing, and fuels innovation.
What Is Zero Trust Security? A Guide for IT Teams
Zero trust security is a framework built on one principle: Never trust, always verify. Learn how zero trust works, its three core tenets, and how enterprise password management fits into a zero trust strategy.

FAQ: How Much Is Phishing Costing My Company, and What Can I Do About It?
Understand how AI is accelerating phishing, what that’s costing your business, and what you can do about it, among other key phishing topics.

Identity Under Attack: Lessons on AI-Driven Credential Risks from Security Experts
Discover 3 key takeaways from security leaders at Dashlane and Morgan Stanley about how AI-driven credential threats are impacting businesses.

Don’t Let Your Credential Manager Become Shelfware: 5 Ways to Increase Adoption
Learn 5 proven strategies IT admins can use to boost credential manager adoption and protect their organizations’ passwords.

How to Build the Case for a Credential Manager: Answers to Common Concerns
To help your organization’s decision makers understand the value of a credential manager, review these 5 common concerns and how to respond.

How to Build the Case for a Credential Manager: The Cost of Doing Nothing
Learn how to build a business case for a credential manager and discover the hidden costs of poor password hygiene, from security risks to lost IT productivity.

