What is Passwordless Authentication, and Why Should You Care?

Passwords are the keys to your digital life. There are few online accounts or apps that you can access without them. Unfortunately, malicious actors don’t have to go far to find these keys. Even if you’re a savvy consumer and take all the right steps to protect your passwords, they can still be compromised if your service provider has a data breach.
That’s why the emerging passwordless authentication trend is so exciting—you’ll be able to stop relying on passwords and eliminate one of the biggest risks to your account security. While it will take some time for this trend to go mainstream, various companies already offer passwordless authentication, which means it’s a good time for you to dip your toes in. Here’s why.
Want to make life harder for scammers?
Check out our free username generator and random password generator tools.
Think you have a strong password? Use our password strength tester tool to put it to the test!
What is passwordless authentication?
Authentication generally involves one or more of these factors:
- Something you know: A secret like a password or an answer to a security question
- Something you are: Facial features, fingerprint, or another form of biometric identification
- Something you possess: Your mobile device, an authenticator tool, or a hardware key
As the name implies, passwordless authentication allows you to authenticate your identity without using a shared secret. You don’t need to create, store, or manage passwords while still being able to log in to your accounts seamlessly. Passwordless authentication reduces the risk of phishing attacks, as there is no Master Password for attackers to steal through deceptive emails or fake phishing websites that deceive users into sharing sensitive credential details.
In the physical world, an equivalent of passwordless authentication is a key card. Instead of entering numbers on a keypad, you simply wave your card to access your workplace, gym, or another area with restricted access.
Besides biometrics and hardware, common passwordless authentication methods in the digital world include:
- Passkey: A passwordless login based on public-key cryptography
- One-time passcode: A passcode or password sent to you by text or email
- Magical link: A login link emailed to you at the registered address
Dashlane is the first credential manager to enable users to create and access their account without a Master Password. Check out what our Senior Product Manager has to say.
How does passwordless authentication work?
Not only does passwordless authentication not share any secrets with the website or app, but it also doesn’t store them with the provider. This is different from passwords, which require an information exchange to verify their accuracy.
As an example, here’s what the passwordless authentication process looks like for passkeys:
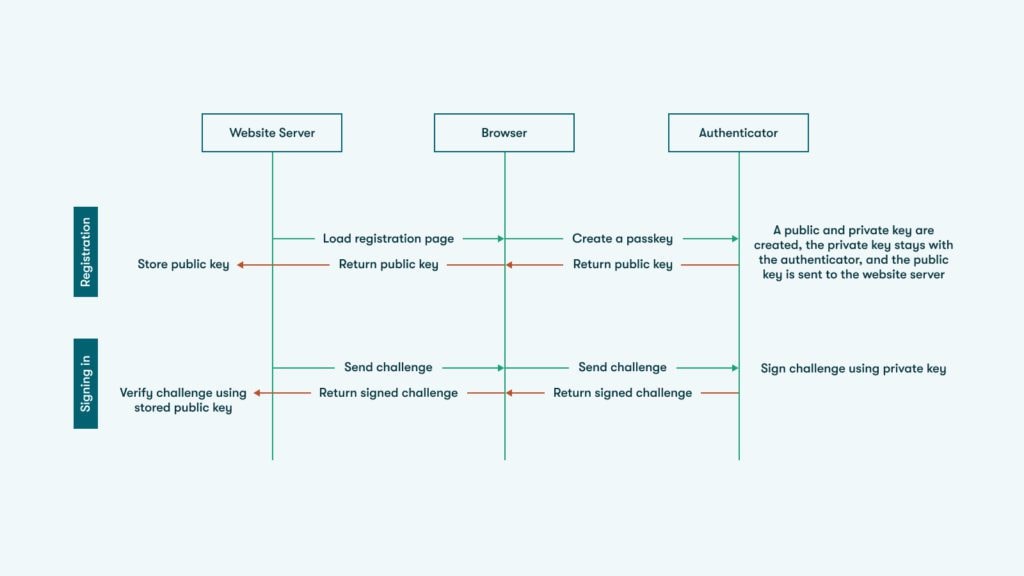
An authenticator—typically a mobile device or a password manager that supports passwordless authentication—generates a pair of cryptographic keys, one public and one private, when you register your new account or enable passkeys on accounts that support them. The service provider or website and your authenticator communicate directly by exchanging the keys.
The public key is sent to the provider’s server for storage, but this key has no value to the attacker, just like your username doesn’t.
The private key stays secret and is stored only in your authenticator. When you try to log in, the server sends a challenge to the authenticator (some random data to prove you’re the one logging in). The private key solves the challenge and sends the response back, essentially “signing” that data with the private key.
The keys are mathematically related, which means that when the signed data is returned to the server, the server can verify it with the public key—but it doesn’t need to know what the key is to validate it.
Why is passwordless authentication more secure?
Passwordless authentication solves many of the weaknesses that passwords are prone to, and that cybercriminals try to exploit. Here are a few of the biggest ones:
- Credential stuffing: Hackers use weak and stolen logins to access other websites, whereas they can’t do the same with passwordless authentication.
- Phishing and social engineering: In the case of passkeys, malicious actors can’t trick you into using the passkeys on a lookalike or fraudulent site because passkeys are unique to the app or website they were created for.
- Stolen credentials: Since passwordless authentication isn’t stored with the service provider, cybercriminals can’t steal those logins by hacking into the provider’s server or database.
- Weak or reused passwords: One of the biggest password challenges is poor hygiene—many people reuse their passwords or create passwords that are easy to remember, and it takes no time for hackers to crack them.
No security method is ever foolproof, but passwordless authentication is numerous notches above passwords when it comes to keeping your information secure. It’s safe to say that passwordless authentication is the way of the future, and that future is finally here. That’s why Dashlane recently launched integrated passkey support.
With Dashlane, you can log in across any website automatically, whether you’ve embraced passwordless authentication or still rely on passwords.
Passkeys are a simpler and more secure way to log in. Learn how Passkeys work and how Dashlane streamlines access.
Sign up to receive news and updates about Dashlane
