How Dashlane’s Bug Bounty Program Helps Us Be More Secure
Originally published in October 16, 2020. Last updated May 5, 2023.
Security is core to a password manager like Dashlane. We build the product to help our customers store their digital identity, credentials, personal information, and payments in a secure and convenient way.
To make sure we maintain the highest level of security, we rely on many cumulative practices and layers of security. Here are a few:
- As we develop the product, each line of code goes through a mandatory internal code review with multiple reviewers from our engineering team.
- We run automated tools to detect potential security flaws in our system.
- Our software development lifecycle is based on the conventions and best practices from standard compliance frameworks, such as OWASP, Google, Apple, and Microsoft guidelines, PCI-DSS, and SOC2.
- Our dedicated security team supports the whole organization in ensuring we have the right security rules.
- We have recently decided to make the source code of our mobile apps publicly available so that more people can audit our code.
- Last but not least, we rely on security bug bounty programs to maximize the number of talented people looking at all our apps and services and raising issues.
What is a bug bounty program?
A bug bounty program is a way for an organization to request white-hat hackers and security researchers look for vulnerabilities and security exploits in their product and reward them with bounties (money) according to the severity of the issue found.
White-hat hackers are ethical computer security experts who specialize in finding security issues. They report security bugs to an organization to provide an opportunity to improve the quality and security of their product. These hackers can do it for free, out of duty to improve security for all, or in exchange for a reward like a bounty. This is often called responsible disclosure: when a white-hat hacker discovers a security issue, they inform the organization so they can correct the vulnerability before it is exploited maliciously or disclosed publicly.
The Dashlane bug bounty program
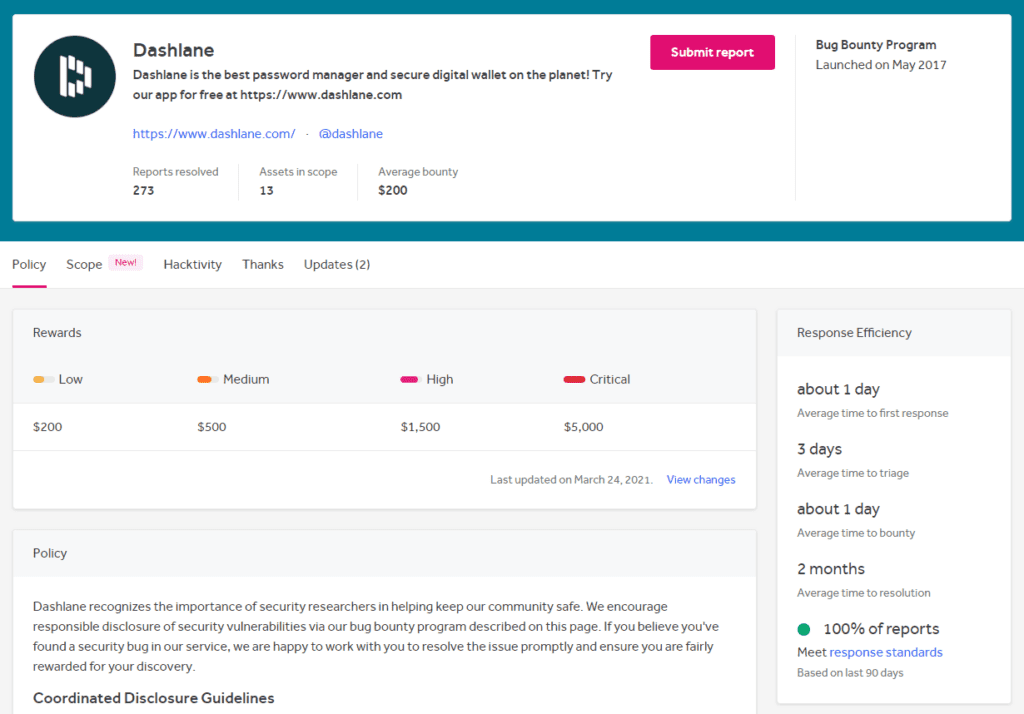
At Dashlane, we began a private bug bounty program on a platform called HackerOne in 2015 and made it public in 2017. HackerOne puts us in touch with thousands of security experts and white-hat hackers. Our Head of Security likes to call them “the Uber of security.” The platform makes it easy to call in help. We can leverage a massive security community and make sure we have many more eyes on our code than if we were to rely only on Dashlane employees or even on third-party security audit agencies.
We started with a private program. On HackerOne, you can start by restricting who can contribute and then progressively ramp up the number of experts who can submit issues. This was important as we learned how to manage the workflow associated with HackerOne submissions.
It’s important to build the right internal structure to evaluate, triage, fix, and reward white-hat hackers within a reasonable time. Program participants expect us to be responsive—otherwise, they will focus on other more attractive programs. Of course, bounty levels are important as well: our bounties range from $200 for a low-severity bug to $5,000 for critical ones. View our recent HackerOne response efficiency and program statistics below.


We continued to refine the precise scope of our program, including what we considered to be eligible submissions and exclusions to the program. This enabled us to avoid getting too many unhelpful submissions or false positives.
Once we were confident we could handle more submissions, we started increasing the number of private invitations to our program until we could make it fully public in 2017.
We’ve also added security resources to our website to make it easier for people to raise security issues. Check out dashlane.com/security/researchers to learn all about our program and how to participate. We love when white-hat hackers and security researchers provide us with concept code or screenshots. That really helps us evaluate and reproduce issues more easily. As a best practice, we also provide a PGP key for you to provide more sensitive information if needed.
Tips to get started
Security is important for everybody. If you work in software development, you should start your own security protocol very early on, even if you are a young startup. It’s easy to do and not that expensive.
- Start as soon as you can with a private program with 50-100 invited white-hat hackers. You will need to offer bounties that align with the market to be attractive.
- During those early days, build the internal process to handle submitted vulnerabilities. Tweak the description and configuration of your program.
- In addition to improving the level of security of your product, use your bug bounty program as a marketing tool. Especially for businesses that sell to other businesses, it adds value to your pitch.
- Ramp up progressively until you are ready to go public.
- At some point, you may observe that the report flow is slowing down. That means you need to up the bounties and communicate to hackers about new features—researchers won’t spend their time in old programs with few easy wins without good incentives.
Get started with Dashlane’s bug bounty program to put your skills to the test and possibly earn some extra money. Happy bug hunting!
Sign up to receive news and updates about Dashlane